Kamal Secrets Are No Fun
Goal
The goal of this post is to use the Kamal Secrets to access the Base64 JSON Key we encoded in Trust 1password with your JSON Key.
Steps
We need to point our Kamal deploy.yml to the KAMAL_REGISTRY_PASSWORD we just created.
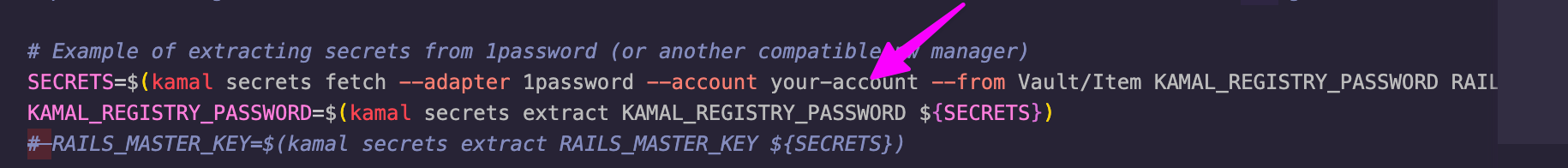
To do so open the .kamal/secrets file in your Rails app. Uncomment out lines 6 and 7, which set the SECRETS and the KAMAL_REGISTRY_PASSWORD variables.
# Secrets defined here are available for reference under registry/password, env/secret, builder/secrets,
# and accessories/*/env/secret in config/deploy.yml. All secrets should be pulled from either
# password manager, ENV, or a file. DO NOT ENTER RAW CREDENTIALS HERE! This file needs to be safe for git.
# Example of extracting secrets from 1password (or another compatible pw manager)
SECRETS=$(kamal secrets fetch --adapter 1password --account your-account --from Vault/Item KAMAL_REGISTRY_PASSWORD RAILS_MASTER_KEY)
KAMAL_REGISTRY_PASSWORD=$(kamal secrets extract KAMAL_REGISTRY_PASSWORD ${SECRETS})
# RAILS_MASTER_KEY=$(kamal secrets extract RAILS_MASTER_KEY ${SECRETS})
# Use a GITHUB_TOKEN if private repositories are needed for the image
# GITHUB_TOKEN=$(gh config get -h github.com oauth_token)
# Grab the registry password from ENV
KAMAL_REGISTRY_PASSWORD=$KAMAL_REGISTRY_PASSWORD
# Improve security by using a password manager. Never check config/master.key into git!
RAILS_MASTER_KEY=$(cat config/master.key)
Kamal comes with an adapter for 1Password. We just need the account and then the path to the password.
You must install the 1password CLI.
Once the CLI is installed. Get your user id by running
op account listCopy the USER ID.
Paste the USER ID on line 6 of .kamal/secrets in place of your-account just after the --acount argument.
Next we need to replace the Vault/Item with the ones we created in Trust 1password with your JSON Key. "Vault" should be keys , which is the name of the 1Password vault we created to store our keys. Item should be project-1, which is the name of the item we created in the keys vault.
Delete the RAILS_MASTER_KEY at the end of the line, which leaves us with:
SECRETS=$(kamal secrets fetch --adapter 1password --account ... --from keys/project-1 KAMAL_REGISTRY_PASSWORD)You can also store your RAILS_MASTER_KEY in 1Password, but that is not in the scope of this guide.
To make sure this is all working, run kamal secrets print. This will print out all the secrets, so make sure you aren't sharing your screen with any bad actors.
> kamal secrets print
SECRETS=\{\"keys/project-1/add\ more/KAMAL_REGISTRY_PASSWORD\":\"ewogICJ0eXBlIjogInNlcnZpY2VfYWNjb3VudCIsCiAg...5LWNvbXB1dGUlNDBkZXZlbG9wZXIuZ3NlcnZpY2VhY2NvdW50LmNvbSIsCiAgInVuaXZlcnNlX2RvbWFpbiI6ICJnb29nbGVhcGlzLmNvbSIKfQo\=\"\}
KAMAL_REGISTRY_PASSWORD=ewogICJ0eXBlIjogInNlcnZpY2VfYWNjb3VudCIsCiAgInByb2plY...nZpY2VhY2NvdW50LmNvbSIsCiAgInVuaXZlcnNlX2RvbWFpbiI6ICJnb29nbGVhcGlzLmNvbSIKfQo=
RAILS_MASTER_KEY=27b...17Conclusion
We now have a connection between our 1Password account, where we store our GCP Base64 encoded JSON key and our Kamal setup. Kamal will use the KAMAL_REGISTRY_PASSWORD to access the Artifact Registry repository where we store our Docker images (Artifact Registry Setup).
Next in Domain Name Setup, lets set up a domain that will point to the VM we created in Baby's First Google Compute Instance.
Member discussion